By Adam Boone,
CMO, Certes Networks.
High-profile hack attacks and data breaches continue to make daily headlines in the waning days of 2014, with a profound effect on enterprise IT projects and the outlook for mobile security in the coming year. What do these ongoing IT security challenges mean for the continued evolution of mobility in the enterprise environment?
#1: BYOD WILL REACH CRITICAL MASS
A majority of companies worldwide now permit employees to use their personal devices such as smartphones, tablets and laptops to access and conduct business with corporate data. A November 2014 global survey conducted by Spiceworks and commissioned by Certes Networks revealed that fully two thirds of the responding enterprises permit BYOD. We predict in 2015 BYOD will reach critical mass as IT is “consumerized” across even highly security-conscious enterprises. This means that the hold-out companies who have prohibited BYOD will be forced to adopt some forms of mobile security and mobile device management to compensate for the consumerization of the IT mix. At a minimum, IT security practitioners will start to plan their security architectures with a worst-case assumption that personal devices are being used, even if corporate policies prohibit such use.
#2: MOBILE ATTACK VECTORS WILL SPIKE
Adam Boone,
CMO
Certes Networks

The deluge of data breaches hitting enterprises around the world in 2013 and 2014 have already cost victims and banks billions of dollars in breach response and cleanup, not to mention lost market valuation. In breach after breach, hackers gained access to internal systems because of faulty network security and inadequate application segmentation. In many cases, these attack vectors were open because the targeted enterprise was attempting to provide access for external parties to internal resources. As more companies adopt BYOD and extended mobile enterprise solutions, we expect attackers in 2015 to exploit both the changes in access control and also the proliferation of personal devices in the hands of mobile employees. In some cases, these breaches will take the form of attackers exploiting a “weak link” represented by personal mobile devices containing sensitive enterprise data that might be exposed to malware or unauthorized applications. In other cases, attackers will take advantage of the enterprise’s modified security posture that is designed to permit BYOD users to access corporate resources.
#3: CRYPTOGRAPHIC SEGMENTATION
One major issue common to most of the breaches coming to light in 2013 and 2014 is that network segmentation and application isolation is simply broken. Enterprises are relying on logical network segmentation to protect sensitive data on internal networks, which is trivially easy for hackers to circumvent. Data traffic encryption is used haphazardly because it brings routers, switches and firewalls to their knees. For example, published throughput test data on firewalls shows that activating even rudimentary encryption causes a typical firewall’s throughput to drop by 50 percent or more. This so in practice enterprises often do not use the encryption functions because of this severe performance hit. But time and again, these trade-offs lead to the security gaps that let hackers steal millions upon millions of data records and credit card numbers. The good news is that enterprises are looking to plug these major holes in 2015. The Spiceworks survey indicates that 56% of enterprises plan to invest in network security upgrades in 2015. We predict that among these upgrades, enterprises will begin to use strong encryption on sensitive traffic more consistently and will deploy cryptographic segmentation to protect internal traffic. This includes traffic to and from mobile devices used both inside and outside the enterprise.
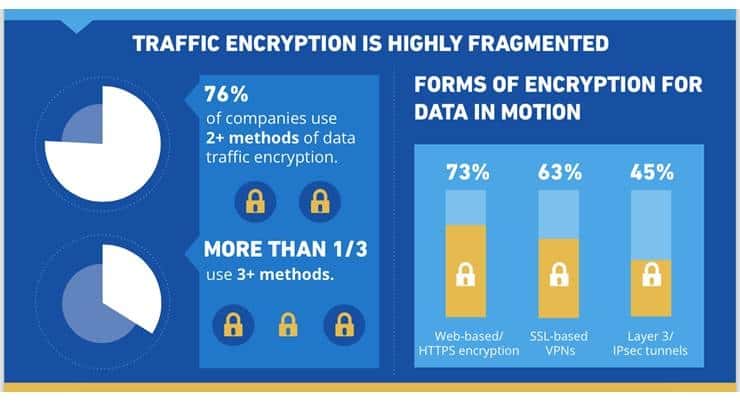
#4: ENTERPRISE-CLASS SECURITY FOR CONSUMERIZED IT
Lastly, we predict that 2015 will see an important positive outcome of the hacking crisis, which will be simplification of security controls and the introduction of enterprise-class security for mobile devices in the BYOD context. A chief security issue around mobile devices is that security controls often are put in place by application developers or the device manufacturers themselves. This means the controls themselves often are not directly integrated into the security architecture of the enterprise. Today, thanks to this “siloed” architecture, IT managers are forced to use multiple systems to try to secure the full path of data from mobile devices to application servers in the enterprise. The Spiceworks survey found that 76% of enterprise IT managers are using two or more entirely separate forms of traffic encryption, and more than a third are using three or more types of encryption. Further, as BYOD programs expand, many of the security controls are “consumer grade” and not enterprise-class. For example, enterprise IT managers want the ability to set cryptographic algorithms, conduct traffic integrity checking, manage key rotation schedules and define and enforce per-user policies that apply across multiple applications and multiple devices. This is challenging when security controls are baked into individual applications and fragmented across devices and networks. We expect to see enterprises in 2015 start to deploy security systems that consolidate and rationalize controls and encryption technologies, reducing fragmentation and bringing mobile device security into the broader enterprise security architecture.
About The Author:
Adam Boone is Chief Marketing Officer for Certes Networks, a leading innovator of solutions for protecting sensitive data in motion. With thousands of deployments in 70 countries around the world, Certes enables enterprises to safeguard data traffic over any network without affecting network performance or leaving gaps to be exploited by hackers. Adam has 25 years of experience in marketing, media and communications and previously held management positions at Marconi, FORE Systems, Subex, Syndesis, CoManage and other leading companies. Learn more at CertesNetworks.com.